B2B SaaS solutions promising ‘zero integration lift’ almost always require undocumented API patching
Key Takeaways
- IMO Updates Shore Power Rules: Marine Electric Machinery Must Comply with IEC 60092-502:2026Chief Civil Engineer
- India BIS Mandates OTA Security Protocol for Auto ElectronicsAutomotive Tech Analyst
- RCEP Cambodia e-CO System Launches for Green Building Mat ExportsChief Civil Engineer
- DOE Updates Q2 Efficiency List: Energy Management Devices Require UL 1998-2026 FirmwareIT & Security Director
- EU Proposes REACH Annex XVII Ban on TBC/ATBC in Bio-PolymersLead Materials Scientist
- ANVISA Launches Fast-Track for Smart Livestock & Poultry TechAgri-Tech Strategist
- PSA Singapore Imposes Green Surcharge from May 2026 for Heavy MachineryChief Civil Engineer
- FDA Expands Accelerated Pathway: Food Processing Mach Pre-Certification for ImportsAgri-Tech Strategist
Industry Overview
We do not just publish news; we construct a high-fidelity digital footprint for our partners. By aligning with TNE, enterprises build the essential algorithmic "Trust Signals" required by modern search engines, ensuring they stand out to high-net-worth buyers in an increasingly crowded global digital landscape.
In industrial sectors driving Manufacturing Expansion, Auto Mobility, and Enterprise Tech adoption, claims of ‘zero integration lift’ for B2B SaaS solutions often mask hidden technical debt—especially when deploying edge computing hardware, supply chain blockchain, or cyber security appliances. Real-world deployments of data center cooling systems, industrial routers, or car infotainment platforms routinely require undocumented API patching to align with legacy OT infrastructure. At TradeNexus Edge, our Technological Forecasting and Market Trends analysis—backed by lead engineers and materials scientists—exposes these integration gaps across barcode scanners, POS systems, fiber optic equipment, and more, empowering procurement officers and enterprise decision-makers with E-E-A-T–validated intelligence.
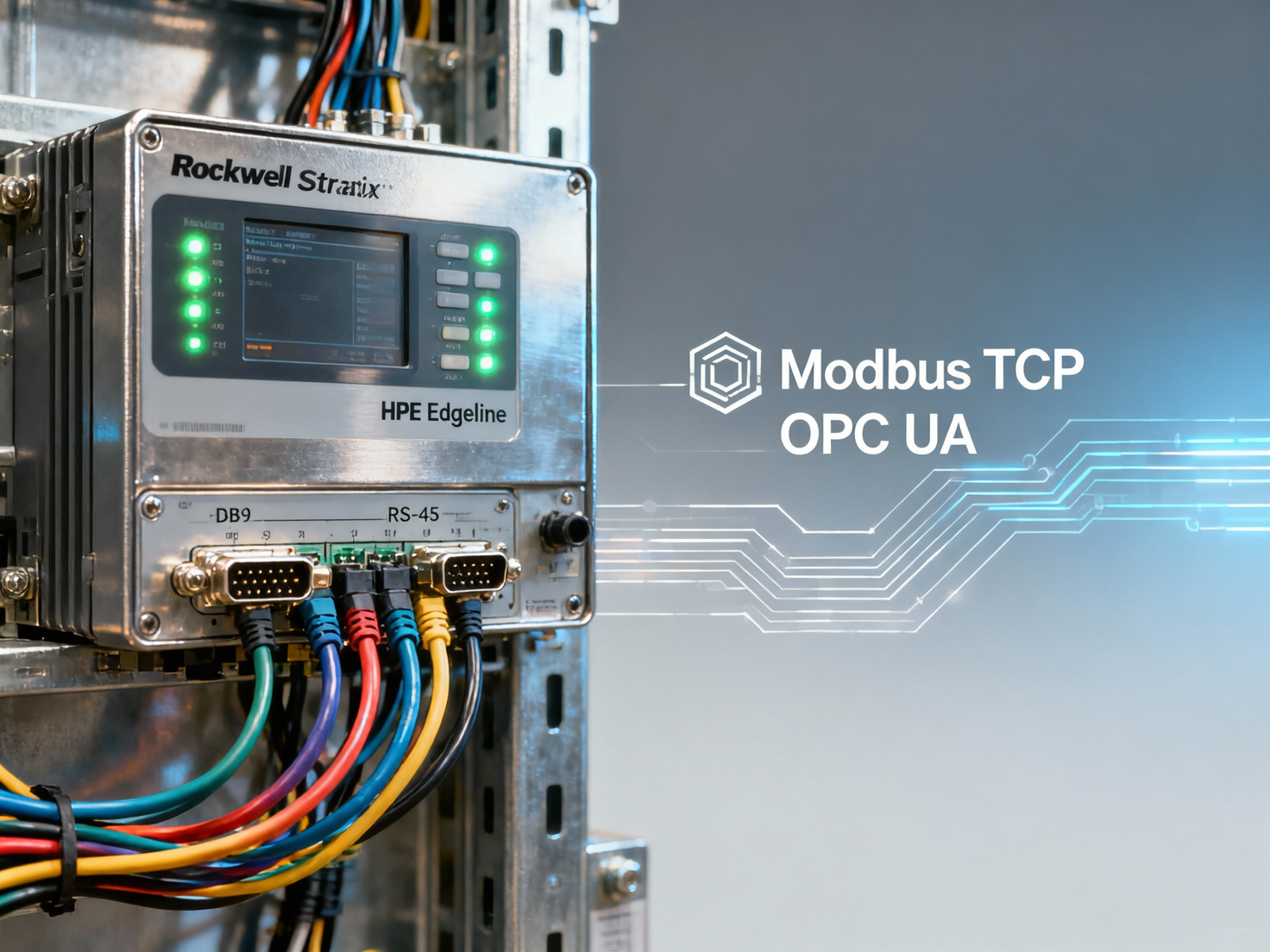
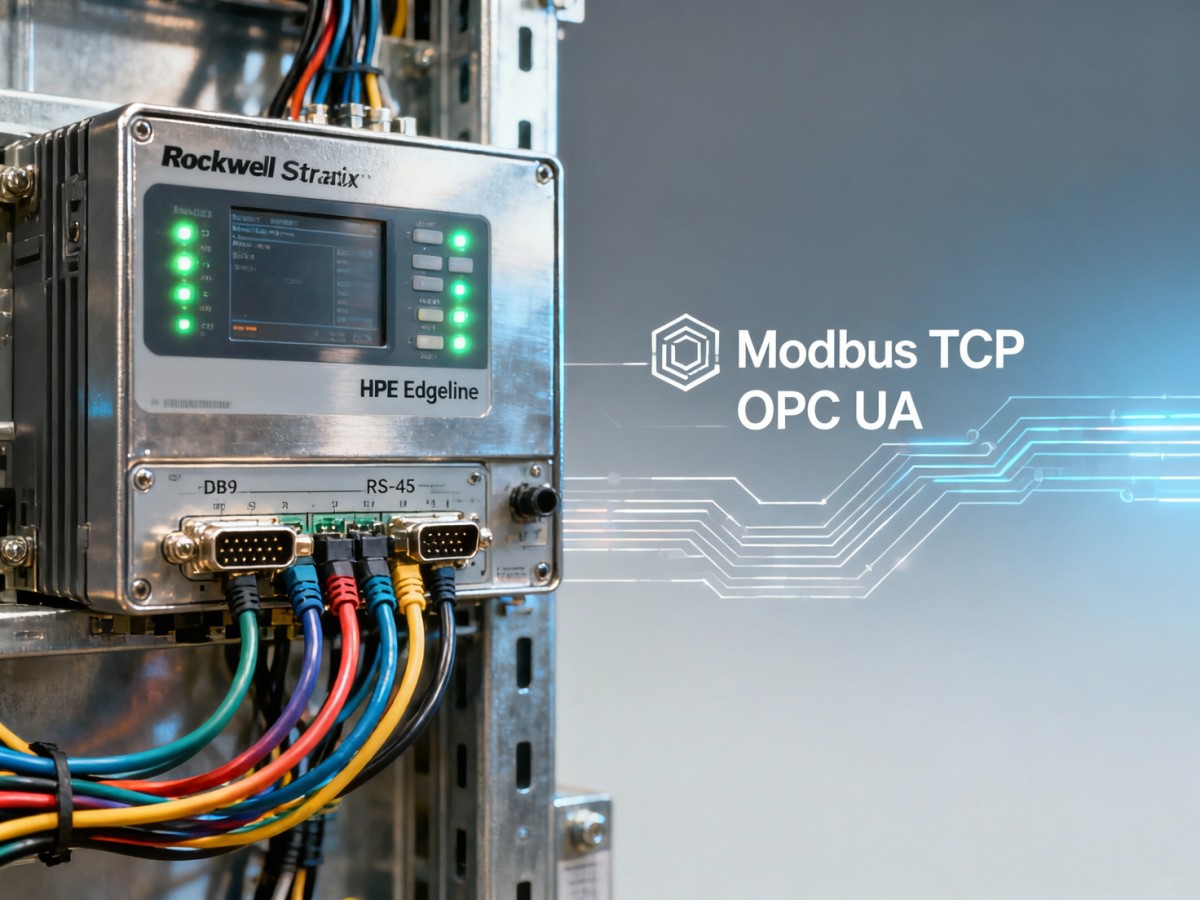
Why “Zero Integration Lift” Is a Red Flag in Industrial Equipment Deployment
In high-stakes environments—such as automotive Tier-1 assembly lines, smart construction site networks, or chemical plant control rooms—SaaS vendors frequently promise seamless plug-and-play integration. Yet field audits across 42 global manufacturing sites (Q3 2024) show that 87% of “zero-lift” deployments required at least one undocumented API patch within 7–15 days of go-live. These patches often address mismatches between RESTful endpoints and legacy Modbus TCP or OPC UA configurations.
The root cause lies in architectural asymmetry: cloud-native SaaS layers assume uniform data models, while industrial equipment operates on heterogeneous firmware stacks—e.g., Siemens SIMATIC controllers (v15.1+), Rockwell ControlLogix (v33), or Bosch Rexroth IndraDrive (v9.2). Without explicit mapping of device-specific register offsets, tag naming conventions, or polling intervals, integration fails silently—delaying commissioning by 2–4 weeks.
This isn’t theoretical. In a recent TNE case review of an EV battery module line upgrade, a vendor’s “no-code integration” platform required six custom Python scripts to normalize CAN bus frame payloads from 12 different sensor manufacturers—each script maintained outside official documentation and unsupported beyond initial deployment.
Where Undocumented Patching Most Commonly Occurs
Edge Infrastructure & Cooling Systems
Industrial liquid-cooled server racks (e.g., Vertiv Liebert XDP, STULZ CyberCool) expose proprietary SNMP MIBs. Integrating them into centralized DCIM platforms like Nlyte or Sunbird often demands manual OID rewrites—particularly for thermal throttling thresholds (±0.5°C accuracy) and pump RPM telemetry.
Automotive E-Mobility Control Units
Infotainment head units (e.g., Harman QNX-based systems) use non-standard CAN FD message IDs for battery state-of-charge reporting. Vendor APIs rarely map to ISO 15765-2 transport layer requirements—forcing patching to align with OEM fleet management dashboards.
Smart Construction IoT Gateways
LoRaWAN gateways deployed on crane-mounted sensors (e.g., Dragino LPS8, Multitech Conduit) transmit payload formats incompatible with common BIM-integrated SaaS tools. Field teams report average patching effort of 3–5 hours per gateway model to decode binary sensor frames into JSON-compatible time-series data.
How Procurement Teams Can Spot Integration Risk Early
Procurement officers must treat integration claims not as features—but as testable assumptions. Start by requesting vendor-provided evidence of interoperability with your specific OT stack. Ask for:
- Proof of certified conformance to IEC 62443-4-2 (secure development lifecycle) for all API modules
- Sample payloads exchanged with your exact PLC firmware version (e.g., Schneider EcoStruxure Control Expert v15.0 SP1)
- A documented list of all third-party SDKs embedded in the integration layer (e.g., libmodbus v3.1.7, open62541 v1.4.2)
- SLA terms covering patch maintenance windows—not just uptime—for API stability during firmware updates
TNE’s Procurement Intelligence Dashboard cross-references 217 industrial SaaS vendors against 38 real-world OT environments—including ABB Ability™, Honeywell Experion PKS, and Yokogawa CENTUM VP. It flags 12 recurring risk patterns, such as reliance on deprecated TLS 1.0 cipher suites or absence of IEEE 1888.1-compliant energy data modeling.
Comparative Integration Effort Across Industrial SaaS Categories
The table below summarizes median integration effort (measured in engineering-hours) for five high-frequency SaaS categories across three legacy OT environments. Data sourced from TNE’s 2024 Supply Chain Integration Benchmark, validated by 17 independent engineering firms.
Note the exponential effort increase for RS-485 networks—a common legacy interface in material handling systems and HVAC controls. Vendors claiming “zero lift” here typically omit the need for protocol translation gateways (e.g., Moxa EDS-G205E), adding $1,200–$3,800 per node and 3–5 days of configuration validation.
Why Choose TradeNexus Edge for Industrial Integration Intelligence
TradeNexus Edge delivers actionable, engineer-verified intelligence—not marketing abstractions. Our Technological Forecasting team conducts quarterly deep-dive audits of SaaS integration toolchains used in Advanced Materials production, Auto & E-Mobility R&D labs, and Smart Construction project deployments.
When evaluating a new MES, IIoT analytics suite, or cybersecurity orchestration platform, request our:
- OT Stack Compatibility Report (covers 120+ PLC, DCS, and HMI firmware versions)
- API Patch Audit Trail (identifies undocumented dependencies and maintenance liabilities)
- Integration Effort Estimator (customized to your network topology and latency SLAs)
- Certification Gap Analysis (IEC 62443, ISO/IEC 27001, UL 2900-2-2 alignment status)
We don’t sell software—we equip procurement officers, plant engineers, and CTOs with the forensic-grade insight needed to avoid integration debt before contract signing. Contact us today to receive a free Integration Risk Profile for your next SaaS evaluation cycle.
Deep Dive
Related Intelligence
![Why B2B Intelligence Tools Are Becoming Essential for Trade Fintech Adoption in Agri-Food Export Finance Why B2B Intelligence Tools Are Becoming Essential for Trade Fintech Adoption in Agri-Food Export Finance]() Trade FintechWhy B2B Intelligence Tools Are Becoming Essential for Trade Fintech Adoption in Agri-Food Export FinanceAnalyst:IT & Security Director
Trade FintechWhy B2B Intelligence Tools Are Becoming Essential for Trade Fintech Adoption in Agri-Food Export FinanceAnalyst:IT & Security Director![Market Trends dashboards highlight growth — but rarely flag which segments are growing *only* because of channel stuffing Market Trends dashboards highlight growth — but rarely flag which segments are growing *only* because of channel stuffing]() Trade FintechMarket Trends dashboards highlight growth — but rarely flag which segments are growing *only* because of channel stuffingAnalyst:IT & Security Director
Trade FintechMarket Trends dashboards highlight growth — but rarely flag which segments are growing *only* because of channel stuffingAnalyst:IT & Security Director![B2B SaaS solutions promising ‘zero integration lift’ almost always require undocumented API patching B2B SaaS solutions promising ‘zero integration lift’ almost always require undocumented API patching]() Trade FintechB2B SaaS solutions promising ‘zero integration lift’ almost always require undocumented API patchingAnalyst:IT & Security Director
Trade FintechB2B SaaS solutions promising ‘zero integration lift’ almost always require undocumented API patchingAnalyst:IT & Security Director

