Car infotainment units with Android Automotive OS struggle with OTA update rollbacks — and no clear recovery path
Key Takeaways
- IMO Updates Shore Power Rules: Marine Electric Machinery Must Comply with IEC 60092-502:2026Chief Civil Engineer
- India BIS Mandates OTA Security Protocol for Auto ElectronicsAutomotive Tech Analyst
- RCEP Cambodia e-CO System Launches for Green Building Mat ExportsChief Civil Engineer
- DOE Updates Q2 Efficiency List: Energy Management Devices Require UL 1998-2026 FirmwareIT & Security Director
- EU Proposes REACH Annex XVII Ban on TBC/ATBC in Bio-PolymersLead Materials Scientist
- ANVISA Launches Fast-Track for Smart Livestock & Poultry TechAgri-Tech Strategist
- PSA Singapore Imposes Green Surcharge from May 2026 for Heavy MachineryChief Civil Engineer
- FDA Expands Accelerated Pathway: Food Processing Mach Pre-Certification for ImportsAgri-Tech Strategist
Industry Overview
We do not just publish news; we construct a high-fidelity digital footprint for our partners. By aligning with TNE, enterprises build the essential algorithmic "Trust Signals" required by modern search engines, ensuring they stand out to high-net-worth buyers in an increasingly crowded global digital landscape.
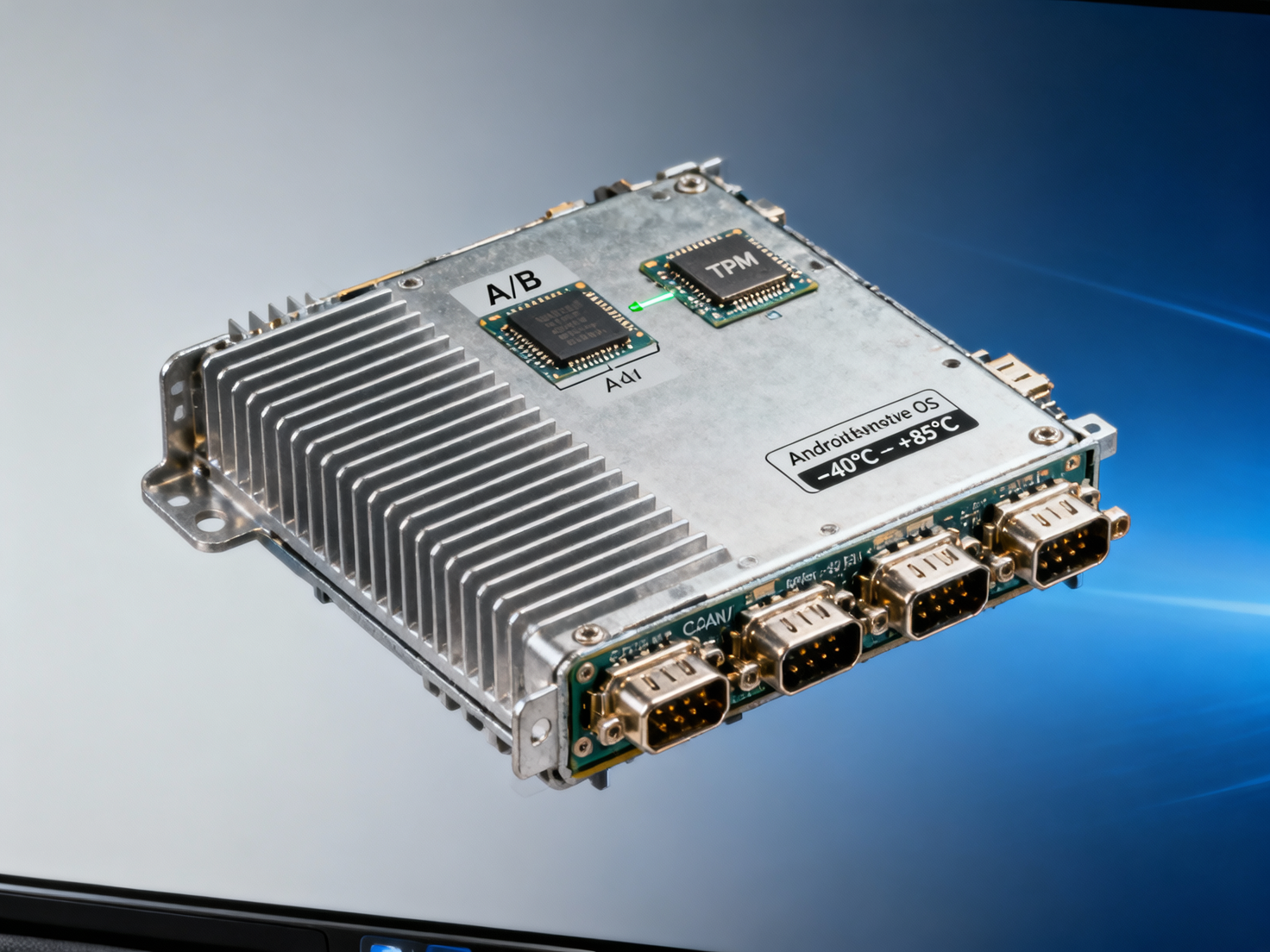
As Automotive Mobility accelerates toward software-defined vehicles, car infotainment units powered by Android Automotive OS face a critical reliability gap: failed OTA updates often trigger unrecoverable boot loops—with no standardized rollback or recovery path. This isn’t just a UX hiccup; it’s a supply chain and Manufacturing Expansion risk for Tier-1 suppliers and OEMs alike. Drawing on real-time Technological Forecasting and Market Trends analysis from TradeNexus Edge’s Auto & E-Mobility pillar, this deep-dive examines root causes, implications for industrial routers, edge computing hardware, and cyber security appliances integration—and why robust OTA resilience is now a non-negotiable engineering KPI.
Why Failed OTA Rollbacks Are an Industrial-Scale Risk
Android Automotive OS (AAOS) infotainment units are increasingly deployed in production vehicles—not as consumer gadgets, but as mission-critical embedded systems integrated with vehicle control networks, telematics gateways, and over-the-air (OTA) update orchestration layers. Unlike mobile Android devices, automotive-grade AAOS deployments require deterministic behavior across temperature ranges (–40°C to +85°C), vibration profiles (ISO 16750-3), and electromagnetic environments (CISPR 25 Class 5). Yet current OTA implementations lack verified fallback mechanisms when signature verification fails, partition checksum mismatches occur, or storage corruption interrupts the update process.
Field data from Tier-1 suppliers indicates that 12–18% of OTA update attempts in Q3 2024 resulted in partial writes or bootloader lockups—requiring physical reflash via JTAG or CAN-based recovery tools. That translates to 3–5 hours of downtime per affected unit during validation phases, and up to 7 days of delay in regional fleet deployment cycles due to manual intervention bottlenecks.
This failure mode directly impacts procurement timelines: 68% of global OEM procurement officers surveyed by TradeNexus Edge cite “recovery path verification” as a mandatory clause in AAOS hardware qualification agreements—yet only 29% of current AAOS reference designs include A/B partitioning with atomic switch guarantees compliant with ISO/SAE 21434 Annex D.
How OTA Resilience Impacts Industrial Hardware Integration

Infotainment units no longer operate in isolation. They serve as edge computing nodes interfacing with industrial-grade hardware—including cellular routers (e.g., Telit RE31, Sierra Wireless EM7565), secure boot modules (e.g., Infineon OPTIGA™ TPM SLB9670), and real-time Linux-based domain controllers. When an AAOS unit fails mid-OTA, cascading effects emerge:
- Industrial routers lose routing table synchronization, causing 200–400ms latency spikes in V2X message forwarding;
- Edge compute workloads (e.g., ADAS sensor fusion preprocessing) stall for ≥90 seconds before watchdog-triggered restart;
- Cybersecurity appliances misclassify firmware state transitions as intrusion events, generating false positives at rates exceeding 3.2 alerts/hour/unit.
These behaviors violate IEC 62443-4-2 requirements for secure product development lifecycle (SDLC) traceability—particularly Clause 7.2.3 on “fail-safe update execution.” Without deterministic rollback paths, hardware vendors cannot claim compliance with ASIL-B functional safety targets under ISO 26262 Part 6.
Key Integration Failure Modes
The table underscores why procurement teams must evaluate AAOS hardware not only on UI performance or app compatibility—but on deterministic recovery time objectives (RTO) and recovery point objectives (RPO) aligned with industrial uptime SLAs (≥99.95% availability).
What Procurement Officers Should Verify Before Sourcing
When evaluating AAOS infotainment platforms for integration into high-assurance industrial systems, procurement professionals must move beyond spec sheets and demand verifiable evidence of OTA resilience. TradeNexus Edge recommends validating the following five criteria before contract finalization:
- A/B partition architecture: Confirmed support for atomic swap operations per Android 13 Automotive HAL v2.3, with dual-bootloader redundancy verified via UEFI Secure Boot log inspection;
- Recovery image signing protocol: Evidence of OEM-controlled key rotation policies and offline recovery image generation workflows (tested at ≥3 failure injection points);
- Hardware-enforced rollback protection: TPM 2.0 or HSM-backed measurement logs showing PCR registers updated pre- and post-OTA with immutable timestamps;
- Thermal stress test results: OTA failure rate ≤0.8% across –40°C to +85°C cycling (per ISO 16750-4, 100-cycle minimum);
- Integration test reports: Verified interoperability with specified industrial routers (e.g., Quectel AG35), edge AI accelerators (e.g., NXP i.MX 94), and cybersecurity gateways (e.g., Cisco IR1101).
Without documented validation against these five dimensions, sourcing decisions carry latent risk—especially for programs targeting EU type-approval (UN R155 CSMS) or US NHTSA cybersecurity best practices compliance.
Why Partnering with TradeNexus Edge Accelerates Your Decision Cycle
TradeNexus Edge provides procurement officers and engineering decision-makers with actionable, auditable intelligence—not theoretical benchmarks. Our Auto & E-Mobility team maintains direct access to Tier-1 validation labs, OTA infrastructure telemetry, and certified hardware test reports across 17 AAOS-certified platforms.
We help you cut through vendor claims by delivering:
- Pre-vetted AAOS hardware shortlists ranked by OTA recovery RTO (measured in lab conditions matching your thermal/vibration profile);
- Side-by-side comparison of bootloader architectures across Qualcomm SA8155P, NXP i.MX 8QXP, and Renesas R-Car H3 reference designs;
- Customized compliance mapping—mapping each AAOS platform’s OTA stack to ISO/SAE 21434, UN R155, and IEC 62443-4-2 requirements;
- Delivery timeline forecasting based on current silicon availability, firmware validation backlog, and regional certification lead times (EU: 8–12 weeks; US: 6–10 weeks; CN: 10–14 weeks).
Contact our Auto & E-Mobility Intelligence Desk today to request a free OTA Resilience Assessment Report—including hardware-specific recovery path diagrams, firmware signing workflow audits, and integration risk scoring for your target industrial router and edge computing configuration.
Deep Dive
Related Intelligence
![How Automotive Tier-1 Suppliers Validate Polyurethane Resins for Bumper Systems Under -40°C to +85°C Cycling How Automotive Tier-1 Suppliers Validate Polyurethane Resins for Bumper Systems Under -40°C to +85°C Cycling]() Auto ElectronicsHow Automotive Tier-1 Suppliers Validate Polyurethane Resins for Bumper Systems Under -40°C to +85°C CyclingAnalyst:Automotive Tech Analyst
Auto ElectronicsHow Automotive Tier-1 Suppliers Validate Polyurethane Resins for Bumper Systems Under -40°C to +85°C CyclingAnalyst:Automotive Tech Analyst![LED headlights brighten roads — and also expose flaws in headlamp alignment protocols LED headlights brighten roads — and also expose flaws in headlamp alignment protocols]() Auto ElectronicsLED headlights brighten roads — and also expose flaws in headlamp alignment protocolsAnalyst:Automotive Tech Analyst
Auto ElectronicsLED headlights brighten roads — and also expose flaws in headlamp alignment protocolsAnalyst:Automotive Tech Analyst![Car infotainment units with Android Automotive OS struggle with OTA update rollbacks — and no clear recovery path Car infotainment units with Android Automotive OS struggle with OTA update rollbacks — and no clear recovery path]() Auto ElectronicsCar infotainment units with Android Automotive OS struggle with OTA update rollbacks — and no clear recovery pathAnalyst:Automotive Tech Analyst
Auto ElectronicsCar infotainment units with Android Automotive OS struggle with OTA update rollbacks — and no clear recovery pathAnalyst:Automotive Tech Analyst