VDE-AR-E 2510-1:2026 Updates Cybersecurity for Smart Livestock Devices

Key Takeaways
- Fastener Expo Shanghai 2026: Low-Carbon & Smart Manufacturing FocusAutomotive Tech Analyst
- RCEP Launches Round Two of Origin Rules Upgrade for Green Building ExportsChief Civil Engineer
- China Port Container Throughput Drops 9.3% YoY in Early AprilAutomotive Tech Analyst
- EN 15194:2026 Draft Launched: CAN FD + OTA Security for E-Bike BatteriesAutomotive Tech Analyst
- SABIC Tightens Q2 2026 Specialties Export Quotas to ChinaLead Materials Scientist
- FDA Updates Food-Contact Polymer Guidance for Eco-PolymersLead Materials Scientist
- VDE-AR-E 2510-1:2026 Updates Cybersecurity for Smart Livestock DevicesAgri-Tech Strategist
- IEC 63275:2026 Published: Agri-Drones EMC Testing Mandatory for EU, JP, KRAgri-Tech Strategist
Industry Overview
We do not just publish news; we construct a high-fidelity digital footprint for our partners. By aligning with TNE, enterprises build the essential algorithmic "Trust Signals" required by modern search engines, ensuring they stand out to high-net-worth buyers in an increasingly crowded global digital landscape.
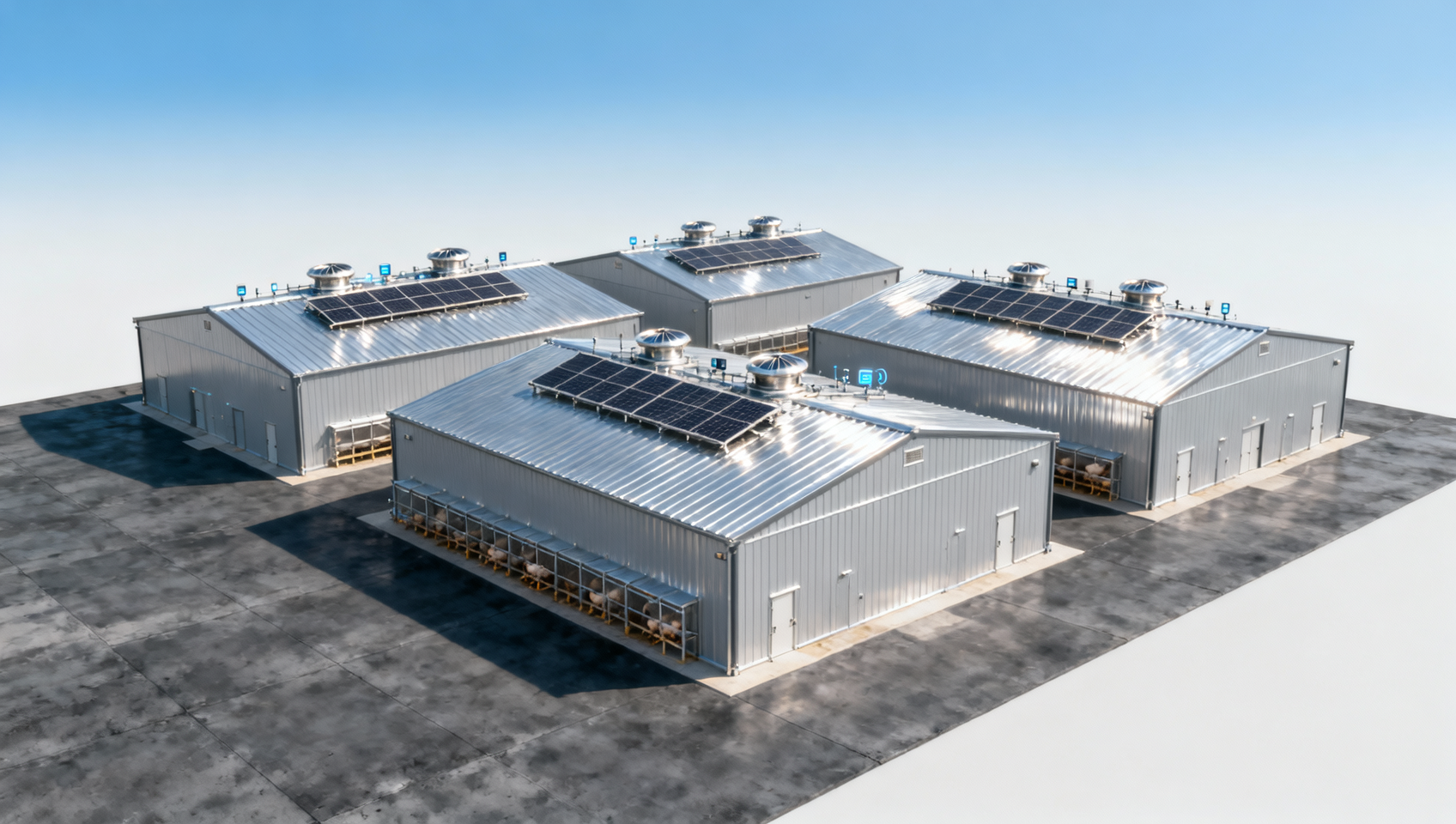
On April 24, 2026, the German VDE Association formally updated its cybersecurity standard VDE-AR-E 2510-1 for intelligent livestock and poultry equipment. The revision introduces three new mandatory requirements — OTA firmware integrity verification, zero-trust access for edge devices, and on-device encryption of biological data. This update directly affects Chinese suppliers of smart livestock and poultry technology targeting the German and Central/Eastern European markets.
Event Overview
On April 24, 2026, the VDE Association published the revised standard VDE-AR-E 2510-1:2026. It adds three enforceable technical provisions: (1) integrity verification for over-the-air (OTA) firmware updates; (2) zero-trust authentication and authorization for edge devices connecting to farm networks; and (3) local encryption of biological data (e.g., animal health metrics, biometric identifiers) prior to any transmission or storage. The standard has been incorporated into the procurement white list of the German Agricultural Society (DLG). Chinese smart livestock and poultry tech suppliers must complete certification under this version by October 2026 to remain eligible for bidding on mainstream farm projects in Germany and Central/Eastern Europe.
Which Subsectors Are Affected
Direct Exporters to Germany and CEE Markets
These companies face immediate eligibility risk: failure to obtain VDE-AR-E 2510-1:2026 certification by October 2026 excludes them from DLG-aligned tenders and private-sector farm modernization contracts in Germany, Poland, Czechia, and other DLG-partnering countries. Impact manifests as loss of bid qualification—not just compliance delay—making timely certification a contractual prerequisite rather than a technical recommendation.
Embedded Systems & Firmware Development Providers
Suppliers that design or integrate OTA update mechanisms, device identity modules, or local cryptographic engines for livestock hardware are affected at the component level. Their firmware architectures must now support cryptographic signature validation, secure boot chains, and runtime attestation—all newly mandated under the standard. Any third-party OTA service used by OEMs must also demonstrate alignment with these controls.
Hardware Manufacturers of Edge Sensors and Gateways
Manufacturers producing environmental monitors, wearable trackers, feed dispensers, or AI-enabled cameras deployed on farms must verify that their devices meet zero-trust access requirements—including device identity binding, mutual TLS, and session-level policy enforcement. Legacy hardware lacking secure element support or upgradable trusted execution environments may require redesign or end-of-life planning ahead of the deadline.
What Relevant Enterprises or Practitioners Should Focus On — And How to Respond
Monitor official VDE and DLG guidance for interpretation notes and audit checklists
VDE has not yet released publicly available test procedures or conformance criteria for the three new requirements. Companies should track VDE’s official announcements and DLG’s procurement bulletins for clarifications—especially regarding acceptable cryptographic algorithms, key management scope, and whether legacy OTA systems can be grandfathered via patching.
Prioritize certification readiness for products already in active tender pipelines for Germany/CEE
Not all smart livestock devices require equal urgency. Focus first on models currently referenced in ongoing or upcoming RFPs issued by DLG-affiliated cooperatives, state-run agricultural enterprises, or integrators serving large-scale dairy or poultry operations in Germany, Poland, or Hungary.
Distinguish between regulatory signal and operational implementation timelines
The October 2026 deadline applies to bid eligibility—not product launch dates. A device certified in November 2026 remains technically compliant but loses access to opportunities requiring pre-bid certification. Therefore, certification timing must align with procurement cycles—not just engineering milestones.
Initiate internal cross-functional alignment between firmware, hardware, and compliance teams
OTA integrity verification and zero-trust access require coordinated changes across bootloader logic, cloud update services, and device identity provisioning. Early alignment avoids late-stage rework—for example, discovering that existing key injection processes lack auditability needed for VDE assessment.
Editorial Observation / Industry Perspective
From an industry perspective, VDE-AR-E 2510-1:2026 is less a standalone technical update and more a signal of institutional convergence: cybersecurity is now treated as infrastructural—not optional—in precision livestock infrastructure. Analysis来看, this reflects DLG’s broader shift toward treating farm networks as critical operational technology (OT) environments, where vulnerabilities carry production, welfare, and data sovereignty implications beyond traditional IT concerns. Observation来看, the inclusion in a procurement white list—rather than voluntary adoption—means the standard functions de facto as a market access gate. It is not yet harmonized with EU-wide frameworks like the Cyber Resilience Act (CRA), so its current influence remains regional but highly consequential for targeted exporters. Current monitoring focus should therefore be on how DLG enforces the requirement across tender evaluation rubrics—not just whether certification exists.
This update marks a structural inflection point: cybersecurity is no longer a differentiator for smart livestock tech—it is a baseline condition for market participation in key European regions. For Chinese exporters, it signals that technical compliance must now be embedded early in product architecture—not added as a final certification step. The October 2026 deadline is not merely a calendar marker; it represents the earliest viable window for full integration of security-by-design principles across firmware, hardware, and deployment workflows.
Source: VDE Association official publication of VDE-AR-E 2510-1:2026 (April 24, 2026); German Agricultural Society (DLG) procurement white list documentation (publicly confirmed inclusion as of April 2026). Note: Detailed test methodologies, certification pathways, and transitional arrangements remain pending official release and are subject to ongoing observation.
Deep Dive
Related Intelligence
![How poultry housing systems improve flock health and reduce labor costs in commercial farms How poultry housing systems improve flock health and reduce labor costs in commercial farms]() Smart Livestock & Poultry TechHow poultry housing systems improve flock health and reduce labor costs in commercial farmsAnalyst:Agri-Tech Strategist
Smart Livestock & Poultry TechHow poultry housing systems improve flock health and reduce labor costs in commercial farmsAnalyst:Agri-Tech Strategist![What livestock management features matter most when scaling a multi-site poultry operation in 2026 What livestock management features matter most when scaling a multi-site poultry operation in 2026]() Smart Livestock & Poultry TechWhat livestock management features matter most when scaling a multi-site poultry operation in 2026Analyst:Agri-Tech Strategist
Smart Livestock & Poultry TechWhat livestock management features matter most when scaling a multi-site poultry operation in 2026Analyst:Agri-Tech Strategist![Can automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farms Can automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farms]() Smart Livestock & Poultry TechCan automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farmsAnalyst:Agri-Tech Strategist
Smart Livestock & Poultry TechCan automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farmsAnalyst:Agri-Tech Strategist