VDE-AR-E 2510-1:2026 Enforces Cybersecurity for Smart Livestock Tech

Key Takeaways
- RCEP Launches Round 2 Origin Rules Upgrade for Green Building ExportsChief Civil Engineer
- IEA Warns AI Boom Strains Grids; China EMS Exports RiseIT & Security Director
- VDE-AR-E 2510-1:2026 Enforces Cybersecurity for Smart Livestock TechAgri-Tech Strategist
- China Port Container Throughput Drops 9.3% YoY in Early April 2026Automotive Tech Analyst
- IEC 63275:2026 Published: New EMC Standard for Agri-DronesAgri-Tech Strategist
- SABIC Cuts Q2 2026 China Export Quotas for Coating Raw MaterialsLead Materials Scientist
- FDA Updates Polymer Food-Contact Guidance Effective Oct 2026Lead Materials Scientist
- EN 15194:2026 Draft Released: EV Bike Battery & Comms UpdatesAutomotive Tech Analyst
Industry Overview
We do not just publish news; we construct a high-fidelity digital footprint for our partners. By aligning with TNE, enterprises build the essential algorithmic "Trust Signals" required by modern search engines, ensuring they stand out to high-net-worth buyers in an increasingly crowded global digital landscape.
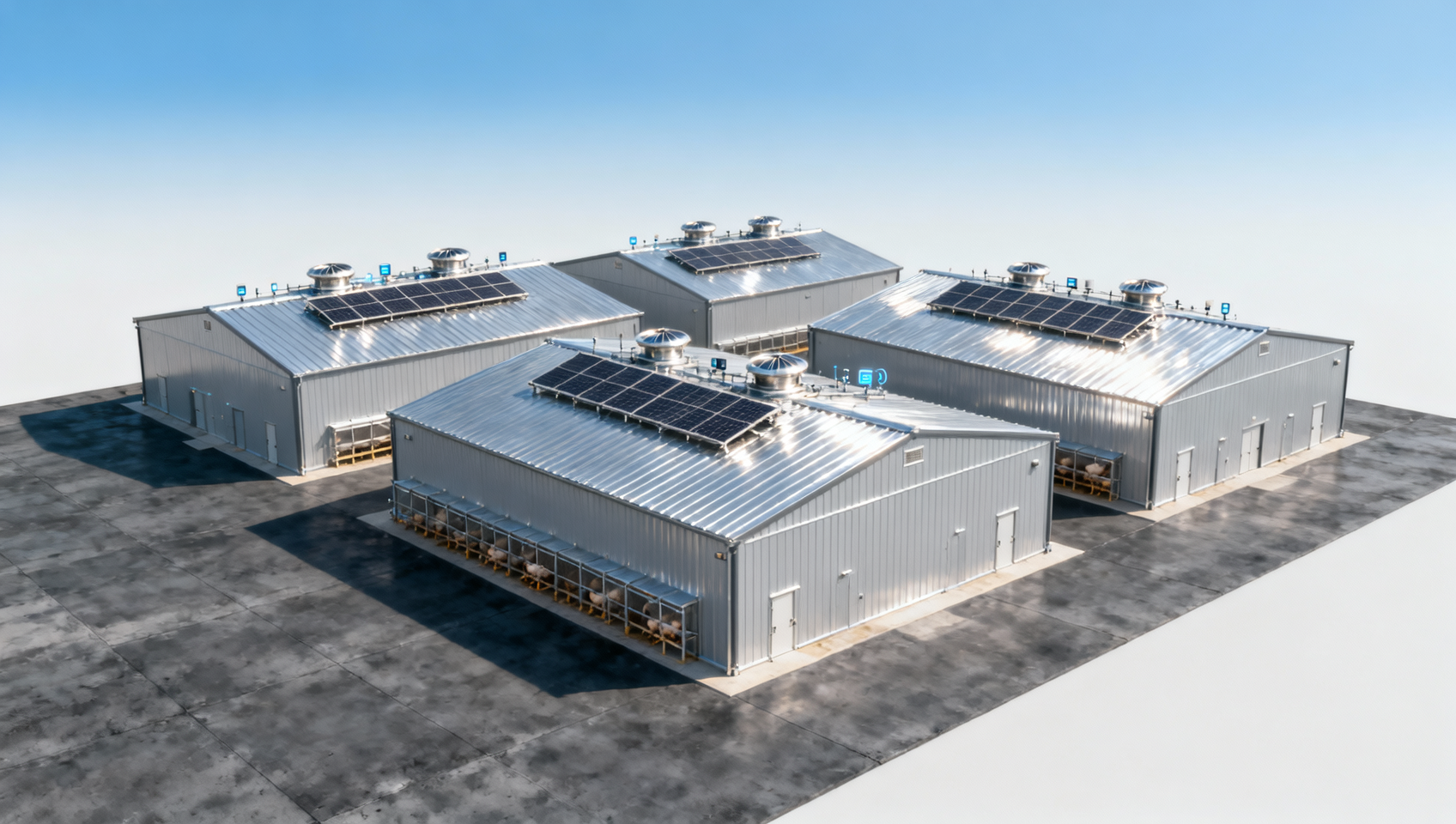
On April 24, 2026, the German Association for Electrical, Electronic & Information Technologies (VDE) released VDE-AR-E 2510-1:2026, upgrading cybersecurity requirements for smart livestock and poultry technology devices—from recommended to mandatory. This update directly impacts manufacturers, exporters, and integrators of intelligent feeding systems, environmental monitoring terminals, and related agri-tech hardware targeting the German and broader EU markets.
Event Overview
The VDE published VDE-AR-E 2510-1:2026 on April 24, 2026. The revised specification mandates cybersecurity compliance for livestock and poultry technology equipment—including intelligent feeding systems and environmental monitoring terminals—effective November 1, 2026. Three new core requirements are introduced: firmware signature verification, secure remote OTA (over-the-air) update auditing, and principle-of-least-privilege access control.
Industries Affected by This Update
Smart Agri-Tech Hardware Manufacturers
These companies design and produce connected devices used in modern barns and poultry houses. They are directly subject to the new mandatory certification. Impact includes revised product architecture (e.g., secure boot implementation), extended development timelines for firmware signing infrastructure, and updated documentation for conformity assessment.
EU Importers & Distributors of Livestock Tech Equipment
Importers placing such devices on the German or EU market must verify compliance before CE marking and market entry. Non-compliant products may face customs rejection, post-market surveillance actions, or withdrawal from sale after November 2026.
System Integrators & Farm Automation Solution Providers
Entities bundling third-party hardware into end-to-end farm management solutions must now ensure each component meets VDE-AR-E 2510-1:2026. This affects integration testing protocols, vendor qualification criteria, and contractual liability clauses regarding cybersecurity assurance.
What Relevant Enterprises or Practitioners Should Focus On — And How to Respond
Monitor official VDE guidance and notified body interpretations
VDE has not yet published detailed application notes or test procedure specifications for the three new requirements. Enterprises should track updates from VDE Testing and Certification Institute and accredited EU notified bodies—especially regarding acceptable cryptographic algorithms for firmware signing and audit scope for OTA processes.
Prioritize validation for devices with remote connectivity and field-updatable firmware
Products featuring Wi-Fi, cellular, or Ethernet interfaces—and those supporting OTA updates—are most immediately affected. Companies should identify high-risk SKUs (e.g., cloud-connected climate controllers or automated feed dispensers) and initiate gap assessments ahead of the November 2026 deadline.
Distinguish between regulatory signal and enforceable obligation
The standard’s enforcement begins November 1, 2026—not upon publication. Until then, VDE-AR-E 2510-1:2026 remains a voluntary reference unless invoked contractually or referenced in national market surveillance plans. Current procurement or R&D decisions should treat it as an imminent requirement, not an active legal barrier.
Update supplier agreements and technical documentation workflows
Manufacturers should revise internal technical file templates to include firmware signature logs, OTA security audit reports, and role-based access control matrices. For OEM/ODM partnerships, contractual terms should explicitly assign responsibility for signature key management and update integrity verification.
Editorial Perspective / Industry Observation
From an industry perspective, VDE-AR-E 2510-1:2026 signals a structural shift: cybersecurity is no longer treated as an optional feature in precision livestock farming, but as a foundational safety and trust requirement. Analysis来看, this mirrors broader EU trends—such as the upcoming Cyber Resilience Act (CRA)—but applies earlier and more concretely to a vertical-specific domain. It is better understood as a policy signal with near-term operational consequences, rather than a fully matured regulatory regime. Continued observation is warranted for how German market surveillance authorities interpret ‘minimum privilege’ in embedded Linux environments and whether harmonized testing methods emerge across EU notified bodies.
Conclusion
This update marks a formal step toward embedding cybersecurity-by-design in agricultural IoT. Its significance lies less in novelty—many of the controls align with ISO/IEC 27001 or IEC 62443 principles—and more in enforceability within a high-value export market. For stakeholders, it is more accurately interpreted as a targeted readiness milestone than a sudden compliance cliff. Proactive alignment with the new requirements supports both market access continuity and long-term product lifecycle security planning.
Information Source
Main source: VDE official announcement of VDE-AR-E 2510-1:2026, published April 24, 2026.
Note: Implementation guidance, test method details, and notified body accreditation status for the new clauses remain under observation and are not yet publicly confirmed.
Deep Dive
Related Intelligence
![How poultry housing systems improve flock health and reduce labor costs in commercial farms How poultry housing systems improve flock health and reduce labor costs in commercial farms]() Smart Livestock & Poultry TechHow poultry housing systems improve flock health and reduce labor costs in commercial farmsAnalyst:Agri-Tech Strategist
Smart Livestock & Poultry TechHow poultry housing systems improve flock health and reduce labor costs in commercial farmsAnalyst:Agri-Tech Strategist![What livestock management features matter most when scaling a multi-site poultry operation in 2026 What livestock management features matter most when scaling a multi-site poultry operation in 2026]() Smart Livestock & Poultry TechWhat livestock management features matter most when scaling a multi-site poultry operation in 2026Analyst:Agri-Tech Strategist
Smart Livestock & Poultry TechWhat livestock management features matter most when scaling a multi-site poultry operation in 2026Analyst:Agri-Tech Strategist![Can automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farms Can automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farms]() Smart Livestock & Poultry TechCan automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farmsAnalyst:Agri-Tech Strategist
Smart Livestock & Poultry TechCan automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farmsAnalyst:Agri-Tech Strategist