IEC 62443-4-2:2026 Released: Firmware Signing & Secure Boot Mandatory for Smart Livestock Tech

Key Takeaways
- FDA Expands FCS Notification to Smart HVAC Components for Food/Pharma CleanroomsChief Civil Engineer
- THE Alliance Reduces Asia-Europe Capacity; Heavy Machinery Freight Costs Rise 12%Chief Civil Engineer
- Smart Agri Expo 2026 Shanghai: 232 Overseas Buyer Groups ConfirmedAgri-Tech Strategist
- Vietnam’s New Food Processing Machinery Import Rules Take Effect Aug 2026Agri-Tech Strategist
- TÜV Rheinland Updates TRGS 220: Thermal Propagation Test Required for EU Battery ExportsAutomotive Tech Analyst
- EU REACH Bans PFAS in Agri-Drones from Oct 2026Agri-Tech Strategist
- SABIC Cuts Q2 2026 Specialty Chemicals Export QuotasLead Materials Scientist
- RCEP Green Origin Rules: Sustainable Building Exports to ASEAN Gain Zero-Tariff, Fast ClearanceChief Civil Engineer
Industry Overview
We do not just publish news; we construct a high-fidelity digital footprint for our partners. By aligning with TNE, enterprises build the essential algorithmic "Trust Signals" required by modern search engines, ensuring they stand out to high-net-worth buyers in an increasingly crowded global digital landscape.
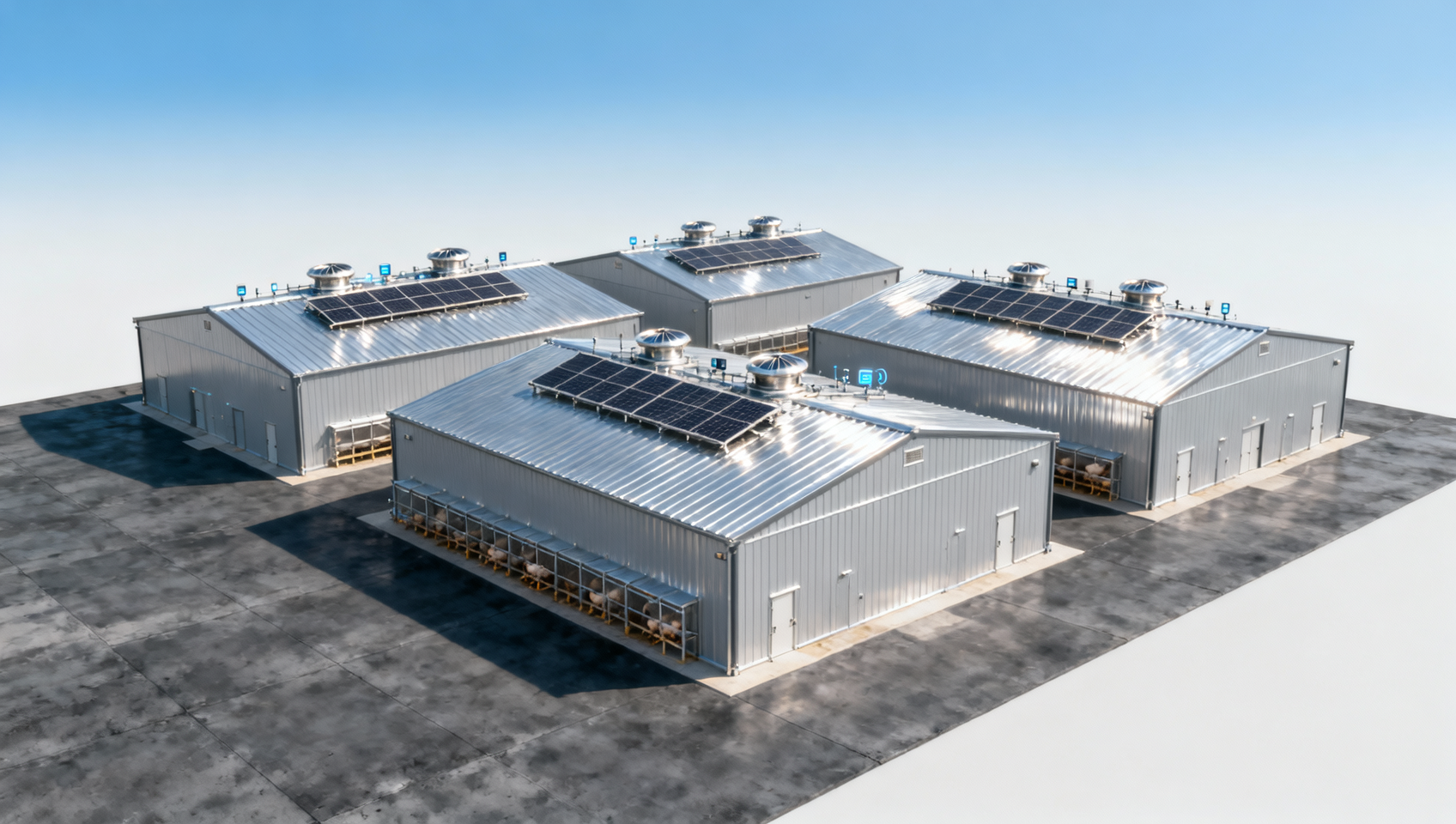
On 27 April 2026, the International Electrotechnical Commission (IEC) published IEC 62443-4-2:2026, a new industrial cybersecurity certification standard directly impacting manufacturers of smart livestock and poultry technology — particularly those exporting to the EU, South Korea, and the UAE. The standard introduces mandatory verification of OTA firmware signing, secure boot, and hardware root of trust, marking a significant shift in market access requirements for connected agricultural IoT devices.
Event Overview
The International Electrotechnical Commission (IEC) officially released IEC 62443-4-2:2026 on 27 April 2026. Titled Industrial Automation and Control Systems Security — Component Security Requirements, the standard explicitly lists over-the-air (OTA) firmware signature validation, secure boot enforcement, and hardware-based root of trust as mandatory audit items. It applies specifically to networked IoT endpoints used in intelligent livestock farming and poultry house environmental controllers. The EU, South Korea, and the United Arab Emirates have formally adopted it as a basis for market access. Chinese manufacturers of smart livestock and poultry technology must complete certification by Q3 2026 to avoid rejection by major procurement partners and potential contract non-compliance.
Industries Affected
Smart Livestock & Poultry Equipment Manufacturers (Export-Oriented)
These companies are directly subject to the new certification requirement. Non-compliance after Q3 2026 may result in shipment refusal by key buyers in the EU, South Korea, and UAE — not merely delayed approvals, but active contract enforcement actions. Impact is concentrated on product lines with network connectivity, including environmental controllers, feed/water automation units, and health-monitoring gateways.
IoT Component Suppliers (Firmware & Hardware Providers)
Suppliers of microcontrollers, secure elements, bootloader firmware, or OTA update frameworks face upstream demand shifts. Device manufacturers will increasingly require components pre-integrated with verified secure boot chains and cryptographic signing capabilities. Legacy components lacking hardware-enforced trust anchors may no longer meet design-in criteria for new export-bound models.
Third-Party Certification & Testing Laboratories
Labs accredited for IEC 62443-4-2 assessment now hold direct relevance to agricultural IoT clients. Demand is expected to rise for test services covering secure boot validation, firmware signature chain verification, and hardware root-of-trust attestation — especially for devices operating under resource-constrained embedded environments typical in farm settings.
What Enterprises and Practitioners Should Focus On Now
Confirm device eligibility and scope of applicability
Manufacturers should verify whether their exported products fall under the IEC 62443-4-2:2026 definition of “industrial automation components” — particularly whether networked functionality (e.g., MQTT/HTTP-based telemetry, remote configuration, or OTA updates) triggers mandatory coverage. Standalone sensors without update capability may be excluded, but this must be confirmed against official IEC guidance, not internal assumptions.
Map existing firmware architecture against secure boot and signature requirements
Teams should audit current bootloader implementations, cryptographic signing workflows, and key management practices. If firmware updates rely on unsigned binaries or software-only signature checks (e.g., SHA-256 hash comparison without asymmetric verification), architectural changes — such as integration with Trusted Platform Modules (TPM), Secure Enclaves, or vendor-provided secure boot SDKs — will be necessary before certification testing.
Engage with notified bodies early — especially for hardware-root validation
Hardware root-of-trust verification often requires chip-level documentation, secure provisioning logs, and physical interface testing (e.g., JTAG lockdown status). Since these elements are typically locked during silicon production, delays in engaging an IEC-accredited lab may extend time-to-certification beyond Q3 2026. Pre-assessment discussions with labs familiar with ARM Cortex-M or RISC-V-based agricultural controllers are advisable.
Editorial Perspective / Industry Observation
Observably, IEC 62443-4-2:2026 functions less as a technical upgrade and more as a regulatory threshold — one that codifies long-discussed security expectations into enforceable commercial terms. Analysis shows this is not a soft recommendation: adoption by three major import markets signals coordinated alignment on baseline cyber-resilience for industrial IoT, with agriculture now explicitly included. From an industry perspective, this standard better reflects a hardening of procurement discipline than a sudden technological pivot — meaning readiness hinges more on documentation rigor and supply chain coordination than on breakthrough innovation. Current attention should focus on traceability: ensuring every signed firmware image can be linked to a certified key hierarchy and every boot sequence verifiably enforces that hierarchy.
Conclusion
IEC 62443-4-2:2026 establishes a binding cybersecurity benchmark for smart livestock and poultry technology entering regulated export markets. Its significance lies not in introducing novel concepts, but in converting established best practices — firmware signing, secure boot, hardware root of trust — into non-negotiable contractual conditions. For affected enterprises, this is best understood not as a future risk, but as an active compliance timeline: Q3 2026 is a firm operational deadline, not a policy horizon. Preparedness now centers on technical mapping, supplier alignment, and early engagement with certification infrastructure — not strategic reconsideration.
Information Source
Main source: International Electrotechnical Commission (IEC), official publication notice for IEC 62443-4-2:2026, dated 27 April 2026.
Points requiring ongoing observation: Official interpretations from EU Notified Bodies regarding scope application to low-power, battery-operated livestock sensors; finalization of national transposition timelines in UAE and South Korea beyond initial adoption statements.
Deep Dive
Related Intelligence
![How poultry housing systems improve flock health and reduce labor costs in commercial farms How poultry housing systems improve flock health and reduce labor costs in commercial farms]() Smart Livestock & Poultry TechHow poultry housing systems improve flock health and reduce labor costs in commercial farmsAnalyst:Agri-Tech Strategist
Smart Livestock & Poultry TechHow poultry housing systems improve flock health and reduce labor costs in commercial farmsAnalyst:Agri-Tech Strategist![What livestock management features matter most when scaling a multi-site poultry operation in 2026 What livestock management features matter most when scaling a multi-site poultry operation in 2026]() Smart Livestock & Poultry TechWhat livestock management features matter most when scaling a multi-site poultry operation in 2026Analyst:Agri-Tech Strategist
Smart Livestock & Poultry TechWhat livestock management features matter most when scaling a multi-site poultry operation in 2026Analyst:Agri-Tech Strategist![Can automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farms Can automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farms]() Smart Livestock & Poultry TechCan automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farmsAnalyst:Agri-Tech Strategist
Smart Livestock & Poultry TechCan automated farming solutions integrate with existing ventilation and feeding hardware on legacy poultry farmsAnalyst:Agri-Tech Strategist